A week doesn’t go by without hearing another story about cybersecurity attacks and hacks.
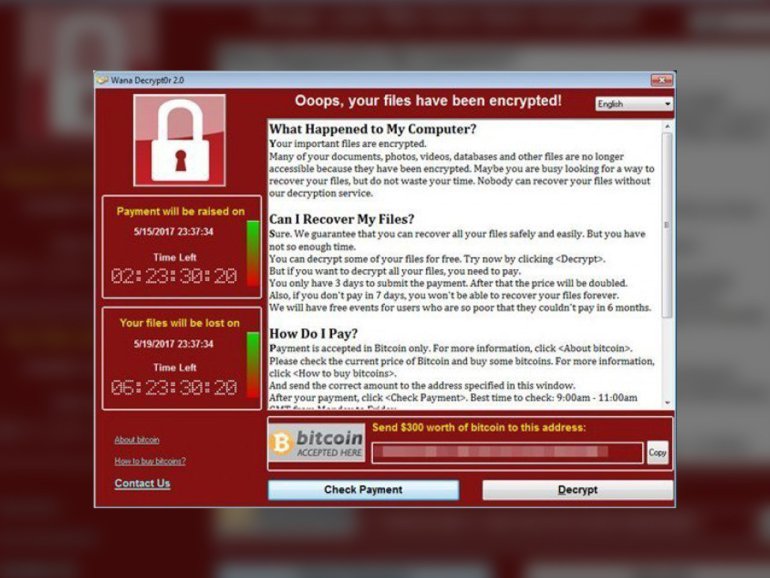
This latest wave of cyberattacks via the WannaCry / Decrytor attack (via Wired UK), follows along the recent Google Docs attack (via Gizmodo) that made waves. While the Google Docs attack was quite sophisticated in building a way to access accounts using email – the recent wave using what appears to be an exploit exposed by the recent NSA leak, has been far more focused on cash than data (But may not have made as much money as you believe, as reported by the Guardian).
The ransomware attack was designed to target vulnerable infrastructure as it spread through hospitals, government, and enterprises – going so far as forcing hospitals to instruct their staff to leave or asking patients and staff to admit only emergency cases. It’s pushed IT consultants and IT service departments to be on full alert as they worked overtime to bring their companies back online and restore data. The attack so far has crippled critical infrastructure within some UK hospitals, and parts of major institutions like FedEx, as IT departments worked hard to stem the attack and assess damage.
Fortunately, it was one researcher that helped put a (temporary) stop to the attack, as detailed by The Next Web. Yet, the warnings have been there along. MIT took a major step recently in urging lawmakers to take urgent steps towards protecting critical infrastructure, on March 28th (via MIT Review).
But the needed steps have not been taken.
Given the disclosures of hacks on Yahoo, the consistent barage of leaks from government intelligence, and attacks across western elections – what are the next wave of attacks we’re likely to see? (via WSJ). And, how do we prepare?
It’s clear that for major public enterprises, institutions, governments, and private companies – there is no foolproof way to be protected. If a large enough attacker decides to attack, it’s quite difficult to counteract. In our day-to-day processes, we haven’t accustomed to the severity of how open our systems are – and how they can quite easily be penetrated with far more sophisticated attacks coming online in the future. Consultants and general IT professionals are also often out of date on best practices, as they work towards maintaining systems. McKinsey notes how most cybersecurity professionals have yet even worked with the CEO to develop new processes or training to implement digital resistance and security protections. (Another reason for more updated practices on leadership training.)
Yet that’s not the only problem – with more platforms, the internet of things, new software products and updates, a greater reliance on third-party tools, the pervasive use of public wifi and an increasingly mobile business class – we’re presenting more opportunities for attackers. The gaps in our systems are increasing, and IT services can’t keep up. These present more problems for consultants and information technology departments to stay up-to-date on vulnerabilities to patch networks, as companies add more services and mobility to their workflow.
But don’t be dismayed. Over coming weeks, we’ll be launching tips and best practices for small and midsize businesses to protect their company’s bottom line, and their staff – including basic training we should all employ. While cybersecurity isn’t foolproof, it is foolish to not do the best we can to protect our data, and have a plan in case of attack, loss, or breach.
Make sure to follow along and subscribe at the right for more, and contact us for a free consultation.
{{cta(‘d2b248a9-dba8-4751-81b7-f45c86154f7e’)}}
